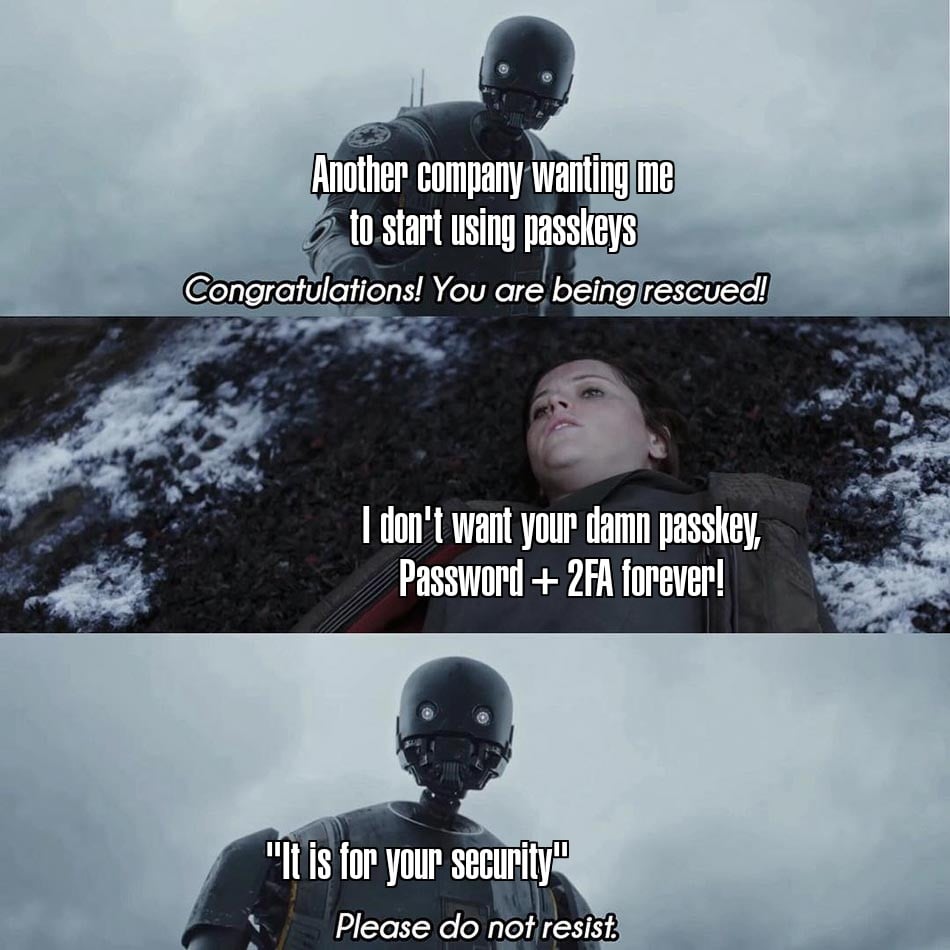
I use passkeys through 1Password and it’s vastly less irritating to me than anything involving passwords, especially 2fa. I really don’t like having to wait for email to arrive or copying down digits from a text message, which seems to be how 2fa typically works 90% of the time.
memes
Community rules
1. Be civil
No trolling, bigotry or other insulting / annoying behaviour
2. No politics
This is non-politics community. For political memes please go to [email protected]
3. No recent reposts
Check for reposts when posting a meme, you can only repost after 1 month
4. No bots
No bots without the express approval of the mods or the admins
5. No Spam/Ads
No advertisements or spam. This is an instance rule and the only way to live.
A collection of some classic Lemmy memes for your enjoyment
Sister communities
- [email protected] : Star Trek memes, chat and shitposts
- [email protected] : Lemmy Shitposts, anything and everything goes.
- [email protected] : Linux themed memes
- [email protected] : for those who love comic stories.
Passkeys are light years ahead of 2fA in user experience. Why do you dislike them?
Security based on devices is one of the positive innovations of smartphones and perhaps the only area where they've improved over the desktop experience.
I very specifically don't want my security tied to my device. Trying to migrate to new phones, and keeping things synced between a phone, desktop, and laptop is why I long ago moved to a password manager. Now, especially in the phone space, getting passkeys to function fully with a password manager ranges from "pain in the ass" to "not actually possible".
I had a botched phone battery replacement once resulting in the phone getting replaced very unexpectedly. It was a nightmare trying to get everything back together because I stupidly used google authenticator, which is tied to the specific phone it’s on. Not tying it to the device is the way to go.
I thought passkeys were supposed to be more secure?
They're using the same standard as FIDO2 / WebAuthn hardware security keys. The protocol is phishing resistant, unlike TOTP and similar one time code solutions.
I prefer the physical ones, because they're easy to organize. Passkey synchronization can be annoying.
It's not for your security, it's for the company's. People suuuuuuuuck when it comes to credentials.
My company insists on expiring passwords every 28 days, and prevents reuse of the last 24 passwords. Passwords must be 14+ characters long, with forced minimum complexity requirements. All systems automatically lock or logout after 10 minutes of inactivity, so users are forced to type in their credentials frequently throughout the day.
Yes people suck with creating decent credentials, but it's the company's security policies breeding that behavior.
I don't get why people get upset at frequently expiring passwords. It's not hard: just write it on a postit note and stick it on your monitor.
Tell them the NIST recommendations for password frequency changes have been really reduced in recent times because it pushes people into other bad password practices. Among all factors, changing the password frequently is the least important.
My company insists on expiring passwords every 28 days, and prevents reuse of the last 24 passwords. Passwords must be 14+ characters long, with forced minimum complexity requirements.
Outdated security practices & cargo culture. Someone should roll up a copy of NIST SP 800-63 to smack them over the head until they read it:
The following requirements apply to passwords:
- Verifiers and CSPs SHALL require passwords to be a minimum of eight characters in length and SHOULD require passwords to be a minimum of 15 characters in length.
- Verifiers and CSPs SHOULD permit a maximum password length of at least 64 characters.
- Verifiers and CSPs SHOULD accept all printing ASCII [RFC20] characters and the space character in passwords.
- Verifiers and CSPs SHOULD accept Unicode [ISO/ISC 10646] characters in passwords. Each Unicode code point SHALL be counted as a single character when evaluating password length.
- Verifiers and CSPs SHALL NOT impose other composition rules (e.g., requiring mixtures of different character types) for passwords.
- Verifiers and CSPs SHALL NOT require users to change passwords periodically. However, verifiers SHALL force a change if there is evidence of compromise of the authenticator.
Maybe ask them their security qualifications & whether they follow the latest security research & industry standards.
I briefly looked into passkeys a while ago, but I think I remember really disliking them because they just seemed like another excuse for companies to lock you in.
Has this changed? With Bitwarden + passwords, I can change to any platform, any device, at any time, and instantly get all my creds moved over securely.
I don't want to be in a situation where I'm locked into using Android, Chrome, iOS, or whatever because I can't move my creds.
I have no idea what a passkey is and I will probably only learn what it is when they become mandatory
I will just use passwords + 2FA for the moment