this post was submitted on 30 Mar 2024
473 points (84.3% liked)
linuxmemes
21321 readers
1106 users here now
Hint: :q!
Sister communities:
- LemmyMemes: Memes
- LemmyShitpost: Anything and everything goes.
- RISA: Star Trek memes and shitposts
Community rules (click to expand)
1. Follow the site-wide rules
- Instance-wide TOS: https://legal.lemmy.world/tos/
- Lemmy code of conduct: https://join-lemmy.org/docs/code_of_conduct.html
2. Be civil
- Understand the difference between a joke and an insult.
- Do not harrass or attack members of the community for any reason.
- Leave remarks of "peasantry" to the PCMR community. If you dislike an OS/service/application, attack the thing you dislike, not the individuals who use it. Some people may not have a choice.
- Bigotry will not be tolerated.
- These rules are somewhat loosened when the subject is a public figure. Still, do not attack their person or incite harrassment.
3. Post Linux-related content
- Including Unix and BSD.
- Non-Linux content is acceptable as long as it makes a reference to Linux. For example, the poorly made mockery of
sudoin Windows. - No porn. Even if you watch it on a Linux machine.
4. No recent reposts
- Everybody uses Arch btw, can't quit Vim, and wants to interject for a moment. You can stop now.
Please report posts and comments that break these rules!
Important: never execute code or follow advice that you don't understand or can't verify, especially here. The word of the day is credibility. This is a meme community -- even the most helpful comments might just be shitposts that can damage your system. Be aware, be smart, don't fork-bomb your computer.
founded 1 year ago
MODERATORS
you are viewing a single comment's thread
view the rest of the comments
view the rest of the comments
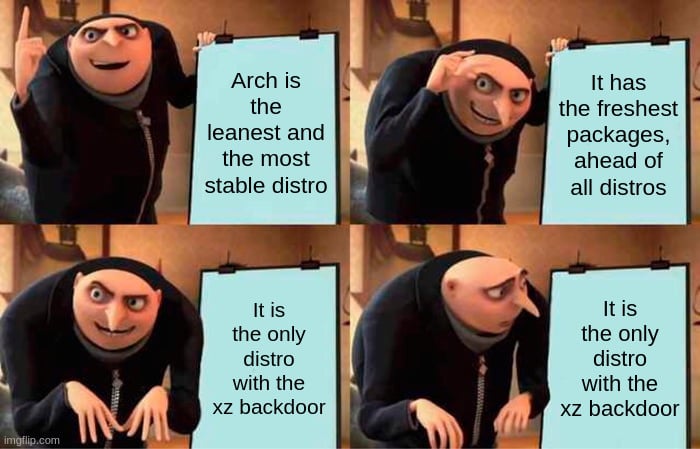
Arch has already updated XZ by relying on the source code repository itself instead of the tarballs that did have the manipulations in them.
It's not ideal since we still rely on a potentially *otherwise* compromised piece of code still but it's a quick and effective workaround without massive technical trouble for the issue at hand.
My only exposure to Linux is SteamOS so I might be misunderstanding something, but if not:
How in the world did it get infected in the first place? Do we know?
From what I read it was one of the contributors. Looks like they have been contributing for some time too before trying to scooch in this back door. Long con.
It seems like this contributor had malicious intent the entire time they worked on the project. https://boehs.org/node/everything-i-know-about-the-xz-backdoor
Wow. That is some read.
edit:I keep thinking my jaw can't go any closer to the floor but I keep reading and my jaw keeps dropping.
HOLY COW!
Basically, one of the contributors that had been contributing for quite some time (and was therefore partly trusted), commited a somewhat hidden backdoor. I doubt it had any effect (as it was discovered now before being pushed to any stable distro and the exploit itself didnt work on Arch) bjt we'll have to wait for the effect to be analyzed.