this post was submitted on 23 Apr 2024
1042 points (97.0% liked)
Memes
46464 readers
3737 users here now
Rules:
- Be civil and nice.
- Try not to excessively repost, as a rule of thumb, wait at least 2 months to do it if you have to.
founded 5 years ago
MODERATORS
you are viewing a single comment's thread
view the rest of the comments
view the rest of the comments
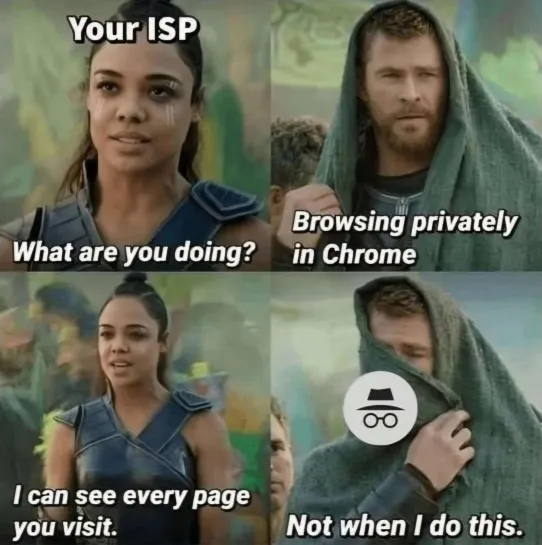
And hopefully in the future they won't even he able to see the domain. I wonder why they never considered giving out certificates for IPs to solve this problem. Seemed like the easiest solution to me.
They need the IP address to know where to forward the packet to. Hard to avoid that without VPN or TOR.
There was a demo for a technology put out recently that circumvents this. I don't remember the exact mechanisms, but it obscured DNS such that your ISP couldn't see the DNS record you requested, and then used a proxy to route traffic before it hit the final endpoint eliminating exposing the IP to your ISP. It worked very similar to a VPN, but without the encrypted connection, and had some speed focused optimizations including the proxy being proximate to your ISP. It was pretty interesting.
It doesn't really help. The ISP needs to route you somewhere to get the data, so they'll need to know who you want to talk to. Even if they don't see the DNS name (like if you used a third party DNS server) they can still associate the IP address with someone.
There's things like TOR and VPNs that can route your information through other third parties first, but that impacts performance pretty significantly.
Depending on where you're going even IP addresses are getting to the point that they aren't helpful. IP addresses are likely to belong to a cloud provider, and unless they are hosting email or a service that requires a reverse record, all you'd get is the cloud provider's information.
Yeah, but often enough multiple sites share a single IP. It would already be better if the ISP (and everyone in between) didn't know whether I wanted pink-fluffy-unicorns.com or hardcore-midget-bdsm.com.
The future is now, old man.
SNI says no.
ECH/ESNI says yes
Yeah, that's what I meant originally. But I still don't know how to enable that in my Apache. My Google-Fu isn't good enough. All I see is ads for CDNs and conflicting information about whether it's supported in Apache or not.
How does that help? You can tell any computer it's Google.com or IP 8.8.8.8. you can tell your device that the other computer is correct, and middle man yourself
Except, we have one key to rule them all, one key to bind them. There's literally a group of people who split the root key among themselves, and scattered it across the world (when they went home). They get together ever year or two, and on a blessed air-gapped computer, unite the key to sign the top level domains again. Those domains sign intermediate domains, and down the chain they sell and sign domains.
If any of these root domains fall to evil, these brave guardians can speed walk to the nearest airport and establish a new order
(I think we actually just started installing all the root and some trusted intermediate domains on every device directly, so I'm not sure if they still bother, but it's a better story)
The solution you're looking for is DNSS, where we encrypt the DNS request too so they can't see any of the url. Granted, they can still look at you destination and usually put the pieces together, but it's still a good idea
Ultimately, packets have to get routed, all we can do is do our best to make sure no one can see enough of the picture to matter. There's more exotic solutions that crank that up to 11, but the trade offs are pretty extreme