this post was submitted on 28 Sep 2023
323 points (75.7% liked)
Games
32926 readers
1705 users here now

Welcome to the largest gaming community on Lemmy! Discussion for all kinds of games. Video games, tabletop games, card games etc.
Weekly Threads:
Rules:
-
Submissions have to be related to games
-
No bigotry or harassment, be civil
-
No excessive self-promotion
-
Stay on-topic; no memes, funny videos, giveaways, reposts, or low-effort posts
-
Mark Spoilers and NSFW
-
No linking to piracy
More information about the community rules can be found here.
founded 2 years ago
MODERATORS
you are viewing a single comment's thread
view the rest of the comments
view the rest of the comments
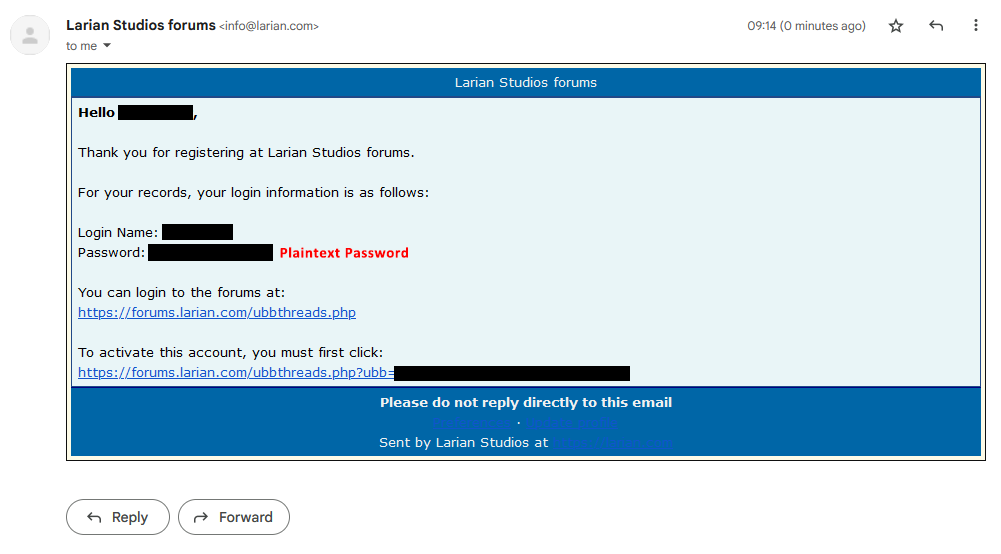
You can also tell if a site does this when they have seemingly arbitrary restrictions on passwords that are actually database text field restrictions.
Especially if they have a maximum password length. The maximum password length should be just the maximum length the server will accept, because it should be hashed to a constant length before going into the database.
I recently created an Activision account during a free weekend event and discovered their password system is completely broken. 30 character limit but refused to accept any more than 12 characters. Kept erroring out with must be less than 30. Once I got it down to 12 it accepted that, but then it complained about certain special characters. Definitely not giving them financial information.
My bank has a character limit, but they don't tell you about it; they just trim the password you've set before hashing + saving it, then when you go to login if you don't trim your password the same way they did, login fails.
I only know this because the mobile app will actually grey out the login button as soon as you enter more than the character limit. The web app just leaves you to be confused.
What an absolutely shitty design.
I had a similar situation with my health insurance company, except I think they added the character limit a while after I had set my password T_T. So, it worked for months, then they changed the mobile app so I couldn't enter a long password... And then eventually they changed the website too and then I couldn't log in at all. Thaaaaanks.
Isn't this also what Windows NT used to do? I feel like I remember encountering this scenario
Doesnt lemmy also do it? I think I ve heard from Ruben at Boostforlemmy that lemmy only treats first 60 characters of your password as a password and the rest gets discarded. [citation needed]
Can't say I've ever tried to use a password quite that long, so I'm not sure.
Not ideal, but trimming it (especially when you're keeping 60 chars) isn't the end of the world. It was just super confusing that the web app doesn't trim it during login as well. There's no indication that your password was modified or what you've entered to login is too long. Just 'incorrect user/pass' despite entering what you've just set. That char limit for my bank is only 16 chars, so it's easy to hit.
It's a big deal IMO, particularly because at login it doesn't do the same. From the user perspective, your password has effectively been modified without your knowledge and no reasonable way of finding out. Good luck getting access to your account.
When a bank does this it should be considered gross negligence.
Kind of.
The official web UI doesn't let you enter more than 60 characters, but doesn't indicate that at all. So you can keep typing past 60 characters but it won't get added to the input field and you can't really see that. If you paste a password into the field, it gets trimmed to 60 characters.
When creating a password, the server checks that it isn't longer than 60 characters and returns an error if so. On login, however, it silently trims the password to 72 bytes, because that's what the hashing algorithm they use supports.
My bank if you get your card number through the app has a dynamic ccv that changes every day so while not perfect is what I use whenever purchasing online
Not really, there are good reasons to limit password length. Like not wanting to waste compute time hashing huge passwords sent by a malicious actor. Or using bcrypt for your hashes, which has a 72 byte input limit and was considered the best option not that long ago. The limit just has to be reasonable; 72 lowercase letters is more entropy then the bcrypt hash you get out of it, for example.
Yes, reasonable limits are fine, I was talking more like 12 or 13 characters max. That's probably indicative of a database field limit, and I've seen that a fair amount because my password manager defaults to 14 characters.