this post was submitted on 20 Jul 2024
1634 points (98.6% liked)
linuxmemes
22213 readers
1627 users here now
Hint: :q!
Sister communities:
Community rules (click to expand)
1. Follow the site-wide rules
- Instance-wide TOS: https://legal.lemmy.world/tos/
- Lemmy code of conduct: https://join-lemmy.org/docs/code_of_conduct.html
2. Be civil
- Understand the difference between a joke and an insult.
- Do not harrass or attack users for any reason. This includes using blanket terms, like "every user of thing".
- Don't get baited into back-and-forth insults. We are not animals.
- Leave remarks of "peasantry" to the PCMR community. If you dislike an OS/service/application, attack the thing you dislike, not the individuals who use it. Some people may not have a choice.
- Bigotry will not be tolerated.
- These rules are somewhat loosened when the subject is a public figure. Still, do not attack their person or incite harrassment.
3. Post Linux-related content
- Including Unix and BSD.
- Non-Linux content is acceptable as long as it makes a reference to Linux. For example, the poorly made mockery of
sudoin Windows. - No porn. Even if you watch it on a Linux machine.
4. No recent reposts
- Everybody uses Arch btw, can't quit Vim, <loves/tolerates/hates> systemd, and wants to interject for a moment. You can stop now.
5. 🇬🇧 Language/язык/Sprache
- This is primarily an English-speaking community. 🇬🇧🇦🇺🇺🇸
- Comments written in other languages are allowed.
- The substance of a post should be comprehensible for people who only speak English.
- Titles and post bodies written in other languages will be allowed, but only as long as the above rule is observed.
Please report posts and comments that break these rules!
Important: never execute code or follow advice that you don't understand or can't verify, especially here. The word of the day is credibility. This is a meme community -- even the most helpful comments might just be shitposts that can damage your system. Be aware, be smart, don't remove France.
founded 2 years ago
MODERATORS
you are viewing a single comment's thread
view the rest of the comments
view the rest of the comments
That's only really true if you're going to be storing the password in a secure vault after randomly generating it; otherwise, it's terrible because 1) nobody will be able to remember it so they'll be writing it down, and 2) it'll be such a pain to type that people will find ways to circumvent it at every possible turn
Pass phrases, even when taken with the idea that it's a limited character set that follows a semi predictable flow, if you look at it in terms of the number of words possible it actually is decently secure, especially if the words used are random and not meaningful to the user. Even limiting yourself to the 1000 most common words in the English language and using 4 words, that's one trillion possible combinations without even accounting for modifying capitalisation, adding a symbol or three, including a short number at the end...
And even with that base set, even if a computer could theoretically try all trillion possibilities quickly, it'll make a ton of noise, get throttled, and likely lock the account out long before it has a chance to try even the tiniest fraction of them
Your way is theoretically more secure, but practically only works for machines or with secure password storage. If it's something a human needs to remember and type themselves, phrases of random words is much more viable and much more likely to be used in a secure fashion.
Generally people don’t memorize private keys, but this is applicable when generating pass phrases to protect private keys that are stored locally.
Leaving this here in case anyone wants to use this method: https://www.eff.org/dice
And if you don’t feel like using physical dice:
https://diceware.rempe.us/#eff
Thanks for that! I recommend anyone who wants to minimize risk to follow their instructions for self-hosting:
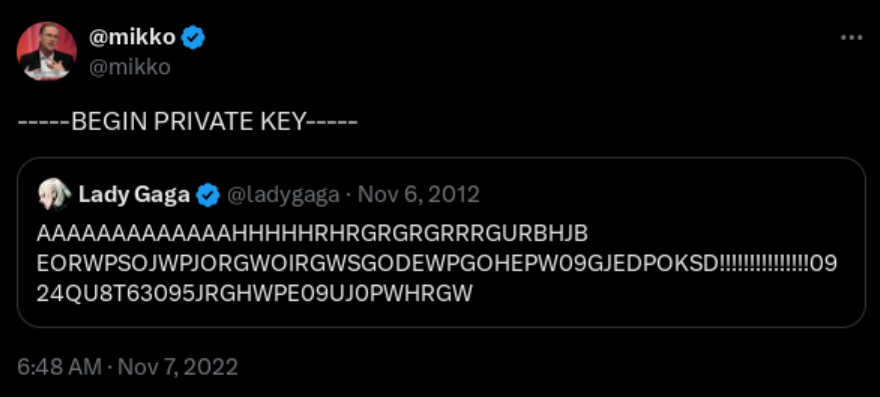
We are talking about RSA though, so there is a fixed character length and it isn't meant to be remembered because your private key is stored on disk.
Yes the word method is better than a random character password when length is unbounded, but creating secure and memorable passwords is a bit of an oxymoron in today's date and age - if you are relying on remembering your passwords that likely means you are reusing at least some of them, which is arguably one of the worst things you can do.
You didn't have to call me out like that.
Okay, that's fair... Not sure how I missed that context but that's totally on me
Most of my passwords are based around strings of characters that are comfortable to type, then committing them to muscle memory. There's a few downsides to this:
If I need to log in to something on mobile and don't have a proper keyboard with me, it's tough to remember which symbols I've used
I share some of my logins with friends and family for certain things, if they call and need to re-enter a password, it's usually impossible to recite it to them over the phone (most of my shared logins have reverted back to proper words and numbers to make it easier for the others)
If I lose an arm, I'll probably have to reset all of my passwords.
But yeah, words alone provide plenty of possibilities. There's a reason cryptocurrency wallets use them for seed phrases.
One small correction - this just isn't how the vast majority of password cracking happens. You'll most likely get throttled before you try 5 password and banned before you get to try 50. And it's extremely traceable what you're trying to do. Most cracking happens after a data breach, where the cracker has unrestricted local access to (hopefully) encrypted and salted password hashes.
People just often re-use their password or even forget to change it after a breach. That's where these leaked passwords get their value if you can decrypt them. So really, this is a non-factor. But the rest stands.
That's fair
It's still a rather large pool to crack through even without adding more than the 1000 most common words, extra digits, minimal character substitution, capitalization tweaks, etc