this post was submitted on 30 Mar 2024
223 points (98.3% liked)
Cybersecurity
5768 readers
96 users here now
c/cybersecurity is a community centered on the cybersecurity and information security profession. You can come here to discuss news, post something interesting, or just chat with others.
THE RULES
Instance Rules
- Be respectful. Everyone should feel welcome here.
- No bigotry - including racism, sexism, ableism, homophobia, transphobia, or xenophobia.
- No Ads / Spamming.
- No pornography.
Community Rules
- Idk, keep it semi-professional?
- Nothing illegal. We're all ethical here.
- Rules will be added/redefined as necessary.
If you ask someone to hack your "friends" socials you're just going to get banned so don't do that.
Learn about hacking
Other security-related communities [email protected] [email protected] [email protected] [email protected] [email protected] [email protected] [email protected]
Notable mention to [email protected]
founded 2 years ago
MODERATORS
you are viewing a single comment's thread
view the rest of the comments
view the rest of the comments
Damn, I was just looking into and learning about the different main compression (gzip, bzip, xz) algorithms the other week. I guess this is why you stick to the ol’ reliable gzip even if it’s not the most space efficient.
Genuinely crazy to read that a library this big would be intentionally sabotaged. Curious if xz can ever win back trust…
Can anyone help me understand xz vs Zstd?
Technically, XZ is just a container that allows for different compression methods inside, much like the Matroska MKV video container. In practice, XZ is modified LZMA.
There is no perfect algorithm for every situation, so I'll attempt to summarize.
The chart below, which was sourced from this blog post, offers a nice visual comparison.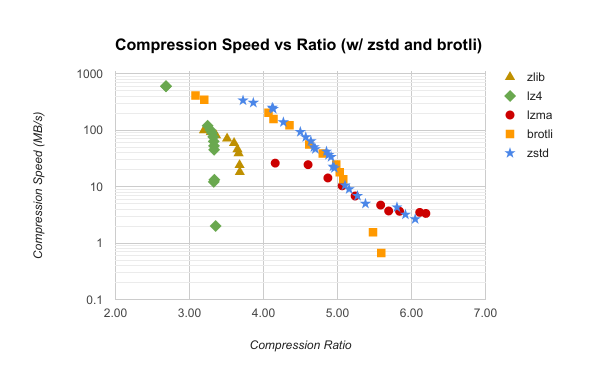
Thanks for this! Good to know that Zstd seems to be a pretty much drop in replacement.
It looks like someone made a Rust implementation, which is a lot slower and only does decompression, but it's at least a rival implementation should zstd get some kind of vulnerability.
Yep that would be me :)
There is also an independent implementation for golang, which even does compression iirc (there is also a golang implementation by me but don't use that. It's way way slower than the other one and unmaintained since I switched to rust development)
Awesome! It's impressive that it's decently close in performance with no unsafe code. Thanks for your hard work!
And that Go implementation is pretty fast too! That's quite impressive.
Sadly it does have one place with unsafe code. I needed a ringbuffer with an efficient "extend from within" implementation. I always wanted to contribute that to the standard library to actually get to no unsafe.
Ah, I saw a PR from like 3 years ago that removed it, so it looks like you added it back in for performance.
Have you tried contributing it upstream? I'm not a "no unsafe" zealot, but in light of the xz issue, it would be nice.
I didn't yet just because I didn't get around to it (and because I am not sure the std lib even wants this feature).
I don't think the two relate. I wouldn't drop any dependency, the ringbuffer is implemented in the same repo.
Yeah, they're not really related. I'm just thinking there might be more scrutiny on compression due to the exploit.
That said, yours doesn't support encoding anyway, so it's kind of moot.
It’s too bad xz is really great for archival.
(/s but I guess kinda not) state-actor weapon compression library vs Meta/FB compression library. Zstd is newer, good compression and decompression, but new also means not as widely used.
On the other hand, whether you trust a government more or less than Facebook/Meta is on your conscience.
Certainly not going back to that /s “state-actor weapon compression library” until it’s picked up by Red Hat or the like…
I guess gzip is good enough for me and my little home lab