this post was submitted on 27 Jul 2024
332 points (95.6% liked)
Linux
48035 readers
1038 users here now
From Wikipedia, the free encyclopedia
Linux is a family of open source Unix-like operating systems based on the Linux kernel, an operating system kernel first released on September 17, 1991 by Linus Torvalds. Linux is typically packaged in a Linux distribution (or distro for short).
Distributions include the Linux kernel and supporting system software and libraries, many of which are provided by the GNU Project. Many Linux distributions use the word "Linux" in their name, but the Free Software Foundation uses the name GNU/Linux to emphasize the importance of GNU software, causing some controversy.
Rules
- Posts must be relevant to operating systems running the Linux kernel. GNU/Linux or otherwise.
- No misinformation
- No NSFW content
- No hate speech, bigotry, etc
Related Communities
Community icon by Alpár-Etele Méder, licensed under CC BY 3.0
founded 5 years ago
MODERATORS
you are viewing a single comment's thread
view the rest of the comments
view the rest of the comments
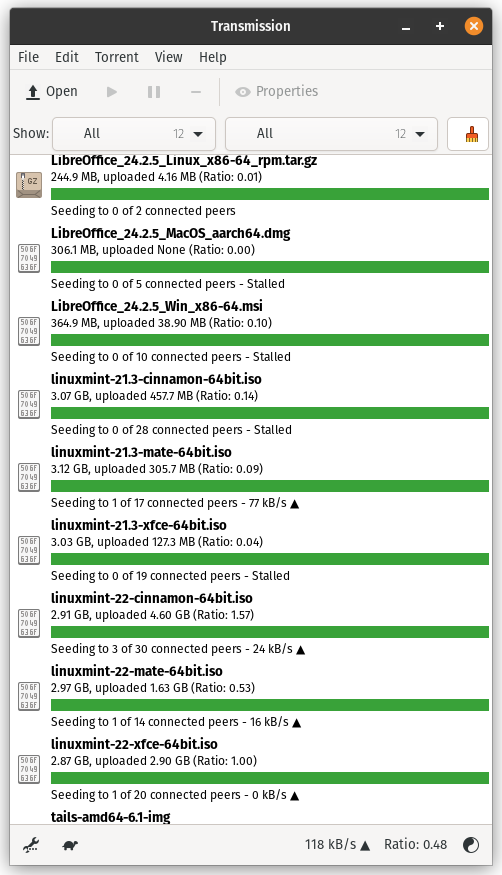
Does anybody download iso's via torrents? Or how to help the actual sites that serve these? Since I trust the source more than torrents.. Especially for an image..
Verifiying the checksum of an iso takes 30 seconds... You don't need to trust anyone
I don't think that is even necessary. If you download the .torrent file from a trusted source it will already contain a secure hash of the final file. Also every piece you receive also comes with a hash that can also be verified through the .torrent file. If you don't trust the source enough to provide a valid .torrent, I don't see how downloading the image directly from them makes any difference. Read more: Official BitTorrent BEP BitTorrent V2 and SHA-256
Well you do need to trust the checksum provided. That is the one you are checking against. Better would be a signature from a key you trust.
In the end a modern torrent is just a hash.
Checksum doesn't verify authenticity. You need to verify the signature
Been on Linux 6 years, never done it. Extra steps
Length of time never means quality of decisions. Always best to validate. So easy to package up malware and farm folks bank accounts.
Hence my threat model hasn't included torrents.