this post was submitted on 11 Nov 2024
-44 points (20.3% liked)
Linuxsucks
236 readers
3 users here now
Rules:
- FOSS advocates and Linux evangelists aren't welcome. -We ask that you block us.
- Moderation is heavy handed. Try to stay on topic (that is LINUXSUCKS!).
- No Complaining Mute the sub if users, content, or rules bother you *it's ok to report rule violations
founded 3 months ago
MODERATORS
you are viewing a single comment's thread
view the rest of the comments
view the rest of the comments
I'm Citrix admin at a newspaper where security is locked down tight.
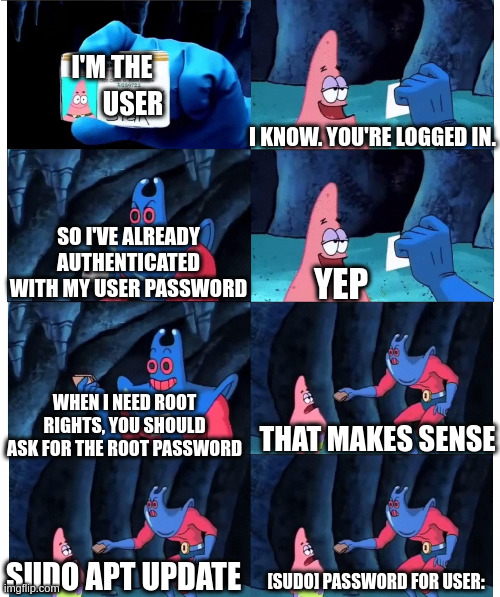
And I feel like you're still misunderstanding my point. Of course, enterprises with increased security do not grant users admin rights with the push of an OK button.
They don't grant them at all.
But the admins at my org authenticate once when they log in (with a password, certificate and second factor).
And they may have to ask for or enable temporarily raised rights for some tasks.
But they do not have to enter their same login password again when they do that. Because there just isn't an attack vector that this would protect against.
Instead, an entirely different login with different password is used, to harden the system against a successful attacker's lateral movement.
Everything you described is possible using sudo, when configured as desired.
Everything you've described is NOT default configuration in Citrix or Windows. I.e. removing local administrative accounts, domain admin accounts with limited permissions and rotating automatically resetting passwords, etc.
I've worked for several enterprises that require UAC password for elevation every time it's needed as the person with elevated permissions (someone who's smarter than the average user) isn't expected to write down their passwords in accessible spaces.
Most enterprises are using third party products to manage the same structure you've described.
You're describing how a lot of enterprises are managing authentication when handled by a person. Not out of the box configuration.
Again, it's a situation that is customized to the usage scenario. What people have suggested you do with your Linux systems.
As noted previously you can configure sudo as desired by the enterprise.
I actually didn't know that elevation with UAC is a thing in (Windows) enterprise, and am still unsure what attack vector it protects against.
But I do see that it seems to make sense to people more knowledgable than me now.
Thanks for the great interaction, by the way.
There are some paranoid environments, and some feel there is a lot to be paranoid about.
I'm not claiming to know everything or to be more knowledgeable. I'm only hoping to persuade you that sudo has benefits, and should be configured for your needs and policies.
I'm glad we can interact peacefully. I hope you have a great day or night!
Actually, no. I just had an emergency alert in on-call service cause there were 3 failed login attempts on one of our fire-walled hosts. 😂
Didn't mean to jinx you. 😂